The greater use of computer technologies to conduct business increases the risk of cybersecurity incidents and data incidents at public companies. To minimize the possibility of exposures, it is necessary for both corporations and auditors to have an understanding of internal controls over financial reporting (ICFR) related to cybersecurity and information technology.
Since 2011, there has been a 300% increase in cybersecurity breaches disclosed by public companies. Due to the proliferation of attacks, accompanied by a variety of challenges associated with implementing effective controls meant to minimize the threats, cybersecurity has emerged as an ongoing corporate governance risk and audit risk.
The design of a robust system of internal controls related to information and data security primarily falls under the corporate governance umbrella. However, organizations may not yet be fully equipped to integrate robust cybersecurity procedures into their internal control environment. EY’s 2020 Global Information Security Survey found that 60% of organizations surveyed did not have a head of cybersecurity who sits on the board or at the executive management level, and only 50% of boards expressed being “somewhat confident” in their organization’s cybersecurity.
External audit professionals also play a role in mitigating cyber threats through both reviews of management’s assessments of ICFR and consulting practices that provide guidance on policies. However, cybersecurity is still an emerging topic in CPA education. In March 2021, the Accounting Program Curriculum Gap Analysis Report found 40% of undergraduate and 41% of graduate programs cover cybersecurity; this includes establishing an understanding of cybersecurity processes and identifying, designing, and monitoring systems.
Material Weakness in Cybersecurity Internal Controls
As an effective internal control environment is the first line of defense for mitigating cyber threats, more education surrounding cybersecurity internal controls would minimize the risk of a public company being exposed to an attack.
Material weaknesses or inefficiencies in these controls – for example, due to a lack of experience or training on behalf of those implementing them – increases the potential for cybersecurity threat exposures.
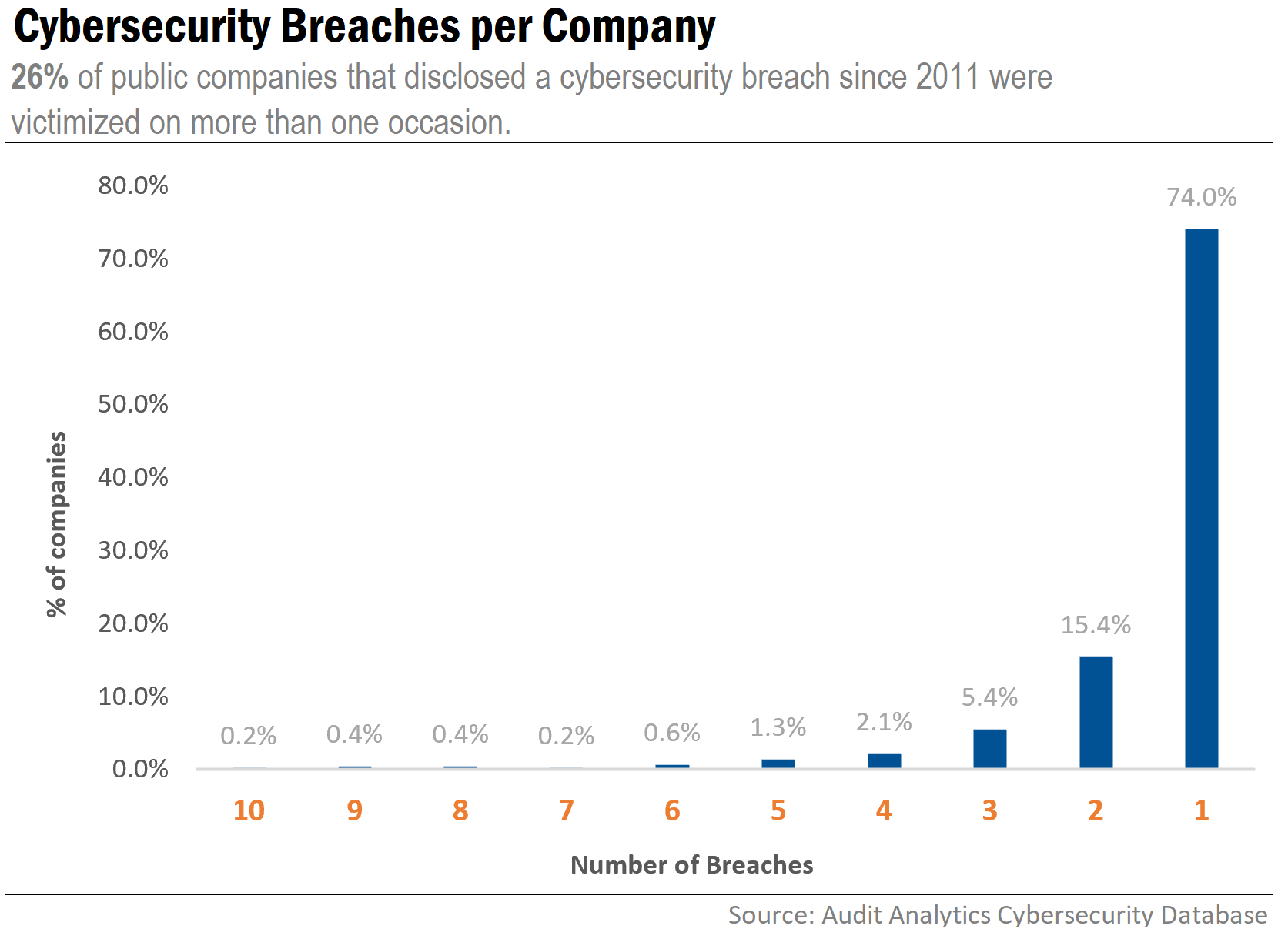
If a material weakness in controls related to cybersecurity is not timely remediated, or a system is not routinely updated to deal with emerging threats, multiple incidents on the same system can occur. Of the companies experiencing a cyber breach since 2011, 26% experienced more than one incident.
The re-victimization of companies is important to note, as it suggests a pervasive pattern of weak cybersecurity controls.
As an example, Helius Medical Technologies [HSDT] became the victim of a business email compromise scheme on two separate occasions, both attributed to deficiencies in controls. The 2017 incident resulted in a fraudulent $0.2 million wire transfer to a third-party impersonator, in a year when the Company recorded no annual revenue. The 2019 incident resulted in a loss of $0.1 million, representing 6.7% of the Company’s annual revenue.
Each attack prompted enhancements to the control system to remediate the weakness, as disclosed in their SEC filings. These improvements, designed to minimize future risks of fraudulent payments, included implementing internal verification measures and enhancing documentation of procedures to ensure that electronic disbursement of funds is allocated to the correct parties at the appropriate times.
While this example underscores the importance of establishing and maintaining effective internal controls to mitigate cybersecurity risks, there is often limited information made publicly available in regards to the impact of a cybersecurity breach on a company’s operations and controls.
Cybersecurity Internal Control Disclosures
There are varying cybersecurity disclosure requirements across states, industries, and regulatory bodies, making information about how companies handle cybersecurity difficult to ascertain, unless certain criteria is met.
SEC guidance has reinforced the importance of disclosing cybersecurity information in current and periodic reports if a potential or an actual cybersecurity incident could have a material impact. Additionally, though not a specific requirement, the SEC previously advised in an investigative report that registrants should specifically consider and assess the potential impact of cyber threats when implementing internal accounting controls.
If a company experienced material impacts from a cyber breach, it mandates disclosure under certain SEC requirements. But if there are no material impacts, detailed information about a breach and any measures taken to bolster cybersecurity protocols in the aftermath of an incident may never be revealed.
Since 2011, roughly 30% of public companies that experienced a cybersecurity incident disclosed impacts in a filing with the SEC; only 4% included a discussion of cybersecurity in relation to controls.
The ongoing digital transformation in the business landscape necessitates changes to the operational and control environment. These changes must be addressed by enhancements to a company’s internal controls; if enhancements are not made in response to the changes, internal controls can become ineffective.
As the prevalence of data breach threats is likely to increase as the world becomes increasing digital, it becomes critical for more professionals, throughout all organizations, to have the necessary tools and education to thoroughly understand the processes used for security of information and minimizing cyber risks.
Interested in our content? Be sure to subscribe to receive our email notifications.